Crosswire Cybersecurity Startup (shutdown April 2024)
Crosswire was an a16z-backed seed stage enterprise security startup that initially began in the identity and access management (IAM) space and pivoted to identity threat detection and remediation (ITDR). However, after two years we’ve since shut down—an experience that offered invaluable insights into the challenges of scaling in the competitive market and the importance of adaptability.
Overview
Joined Crosswire as the founding designer after they received $6 million in seed funding from Andreessen Horowitz and General Catalyst
Role
Lead designer responsible for designs across multiple product pivots, design system, sales demos, and marketing website
Initial Direction
Initially, our focus was on Identity and Access Management (IAM), which allows organizations to manage and control access to their systems and data. IAM ensures that only authorized individuals have the appropriate access, safeguarding sensitive information and maintaining security by restricting access for unauthorized users.
“As a security engineer I want to simplify complex identity and access management tasks, reduce security risks, and ensure compliance with industry regulations."
Partnership with MetaLab
Before I joined, Crosswire partnered with a design agency, Metalab, for their initial access management product vision and foundational research.
Initial IAM Mocks
The goal of this initial direction was to empower security analysts/ engineers to easily create policies to streamline enterprise software access and approval flows.
Creating Access Policies
Security analysts can establish access control policies that define who can request specific software systems based on their roles and responsibilities within the organization. These policies also outline the approval process for granting access.
Requesting Software Access
Employees can request access to software they need to be productive at work.
Viewing & Approving Access Requests
Managers and app admins are able to view requests and approve or deny access.
Initial Research
MetaLab led initial rounds of foundational research & concept testing.
Overview
10 prospective users
Security folks with varying experience levels
75 minute sessions - open discussion and concept review
Key Findings
Security buyers and end users do overlap
Security folks range from lower level to CISOs and CTOs who wear multiple security hats and are involved in the decision making process.
Existing setups are complex and involve many manual processes, there is a need for improvement
Current setups consist of several tools including Okta and/or Microsoft, which increases security through 2FA and SSO.
Biggest pain point is not having a centralized overview to support security best practices and reduce risks
It’s important for users that access to all systems is centrally managed and tracked, but most don’t have a singular overview of IAM, which makes granting/revoking, auditing, and risk management cumbersome.
Users use automation today and want it to become a key piece to simplify internal processes, but are also skeptical of automated processes
Users are open to automated processes to reduce manual work but haven’t found the right resources for successful implementation across orgs.
Policy creation is not a single user process and faces challenges
Policies are created collaboratively, often initiated by executive level. Most teams users run into issues including policies being too generic, having too many policies to properly maintain, and difficulty enforcing policies across the org.
Updates & Additional Feature Designs
After initial design direction and research handoff from MetaLab, I jumped into iterating and expanding on our product offering in collaboration with the cofounders. We were beginning to have potential customer conversations who directly asked for more flexibility in policy creation.
Additional Jobs-to-be-done as a Security Analyst & Corresponding Features:
Centralized Policy and Metrics View: Security analysts need a comprehensive, real-time view of access management policies and metrics to evaluate compliance, detect anomalies, and decide on corrective actions efficiently.
Rule Customization: Security analysts need to configure access rules based on group, role, user, or associated identifiers to control who can request access to specific software, ensuring proper governance and alignment with security policies.
Automated Role-Based Access: Security analysts need to automate the approval process for access requests based on user roles and groups to minimize manual intervention.
Temporary Access Control: Security analysts need to define time-limited access for users and automate access revocation after a set period, ensuring compliance with least privileged access policies.
Making Sense of the App
Information Architecture breakdown of near-term and future components of the web app as well as who can access each section separated by dashboards and reports, managing access requests / policies, accessing software applications, viewing people, and customization settings.
Sales Demos & Conversions
Since much of this was still in development, I created clickable sales demos for the sales team to present to potential customers — and we secured our first two paying clients!
Product Pivot to Identity Threat Detection & Response (ITDR)
In early-stage startups, achieving product-market fit is crucial. The co-founders dec pivot from access management to a more dynamic and innovative cybersecurity space: identity threat detection and response.
Reasons for Pivoting
The access management market is highly saturated due to the growing significance of cybersecurity and regulatory compliance.
Identity has become the center of modern attacks, with 90% of organizations having experienced some sort of identity attack in the past year.
By focusing on threat detection, we can emphasize the urgent need for action and strengthen our sales conversion strategy.
The industry is expected to expand significantly, growing from $12.8 billion in 2024 to $35.6 billion by 2029.
What is ITDR?
ITDR (Identity Threat Detection and Response) focuses on identifying and mitigating threats related to user identities and access privileges. It involves:
Monitoring user behavior: Identifying unusual activities or patterns that could indicate a security breach.
Detecting identity threats: Identifying compromised accounts, privileged access abuse, and other identity-related risks.
Responding to incidents: Taking swift action to contain and remediate security breaches, such as disabling compromised accounts or resetting passwords.
ITDR is a critical component of a comprehensive cybersecurity strategy, as it helps organizations protect their sensitive data/systems and is the next of defense if something is compromised.
74% of breaches involve the human element, which includes social engineering attacks, errors and misuse, and 49% of breaches involve compromised identity
- 2023 Verizon Data Breach Investigation Report
Jobs to be done reframed in ITDR context
As a security analyst/engineer I want to:
Detect unauthorized access attempts quickly in order to minimize risk and respond to potential breaches early
Investigate identity-related security incidents efficiently in order to resolve threats faster with accurate and actionable data
Ensure compliance with security regulations in order to maintain adherence to cybersecurity standards and policies
Reduce alert fatigue in order to focus on critical identity threats and prioritize high-risk incidents
HMW:
Distinguish level of risk to alert users without creating additional noise?
Define what security baselines/checks to display (across SOC2, NIST, ISO)?
Display threats and risks with enough context for users to understand level of threat and what action to take?
Connect to other integrations for a cohesive platform?
Determine what remedial actions users can or cannot take?
Introduce automated workflows to minimize manual checking without losing trust?
Understanding the Space & Design Explorations
Example User Flow
In this user journey, Crosswire ensures preventative security measures are in place, detects unusual activity, and then empowers security analysts to investigate, take action, and report on the incident.
Grouping Posture Risks & Threats
Collaborated with cofounder to think through posture risks vs threats and considered how we would display them:
Categories to begin with
Posture risks: any sort of non-compliance or misconfiguration
Weak passwords
Discrepancies in HR systems
Overprivileged access
Insecure APis
Incorrect set up of cloud services
Identity security threats: security events with a timestamp triggered by a user action
Unusual activity: e.g. unrecognized device, suspicious IP address, unusual location
Multiple failed login attempts
Sign in from multiple locations
Suspicious privilege escalation or new application authorization
Competitor Takeways: Wiz, Orca, and OORT
Key takeaways based on similarities of their platforms:
Combine posture and threat detection in a unified alert/issues page, providing visibility into both areas simultaneously instead of focusing on just one.
Present a dashboard overview of various threat types, with the option to drill down into detailed information for deeper analysis.
Offer an attack path timeline or narrative to help users trace the progression of attacks and understand how they unfolded.
Organize threats at a high level with filtering options, enabling users to dive into specific threats for more detailed insights and related events.
Displaying Posture Risks & Threats
This table provides an overview of all posture risks and threats in one location, allowing users to filter by type and drill down into each threat for more detailed information and remedial actions.
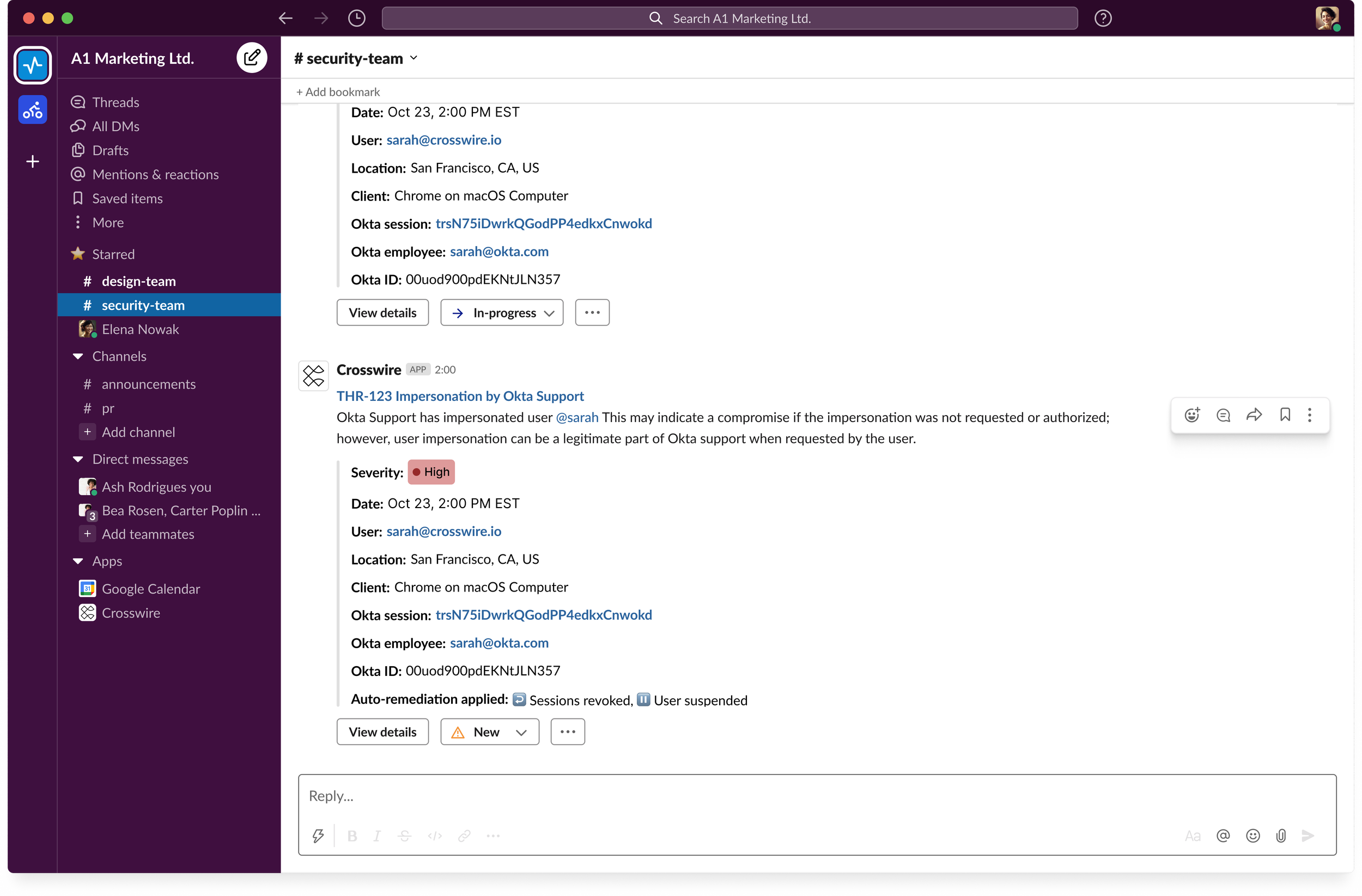
Optimizing for Efficiency with Integrations & Alerts
Potential customers expressed frustration about needing to log into yet another platform. By allowing them to choose their preferred notification system to integrate with—Slack, Teams, and/or Email—they can receive important alerts and take immediate action.
Exploring Rules for Remediation (Future)
I also explored allowing users to set custom threat triggers and decide how to handle remediation to allow more flexiblity. However, after discussing with advisors, CISOs, and our cofounders we decided we needed to simplify the flow to minimize upfront work for users and reconsider this for the future.
MVP Product Prototype
After collaborating with co-founders and gathering feedback from advisors and CISOs, here’s a walkthrough of the MVP prototype that covers the following:
Immediate alerts with minimal noise: Security analysts receive instant notifications about identity risks and threats, enabling them to investigate and take action while minimizing noise.
Overview with threat and risk tables: Users can easily assess their organization's security posture through comprehensive threat and risk tables, allowing for detailed drilling and sorting of information.
Understanding detection and remediation: To encourage transparency and trust, security analysts can view and enable/disable detection across threats and risks as well as decide if they want to set autor-emediation when each one is detected.
Viewing user risks: Analysts can access a detailed list of the organization’s employees, assessing their individual risk levels and understanding their impact on overall organizational security.
Note: Expand prototype below to full screen to view
Metrics & Feedback
We utilized Fullstory and Google Analytics to track most commonly detected threats, as well as confused user behavior or frustrations. This helped us identify bugs and fine tune UX.
For example, we realized users were getting frequent notifications from unusual sign in due to VPNs, so we tailored the threat parameters.
In addition, users were trying to see information about a threat without having to drill into another page, so we added a side peek view.
Shut down & Reflection
Difficult Decision to Discontinue Crosswire Services
After a couple of years with multiple iterations, pivots in direction, reorgs, and layoffs—our cofounders made the very difficult decision to shut down Crosswire in April 2024 and pursue their own separate paths in the security and ops space.
Reflection
Transitioning from a large enterprise software environment at Salesforce to a seed-stage startup as the sole designer was a transformative experience. It required me to take on various roles, from website design and expanding the design system to creating all sales and marketing collateral, all while collaborating closely on product design with co-founders and developers. Here are some key takeaways:
Leverage your network for quick research and feedback: We frequently reached out to existing customers, advisors, and CISOs for iterative feedback on our concepts. This was essential since we lacked a dedicated user pool for more formal research sessions.
Iterate rapidly and avoid overcommitting: Crosswire invested considerable time and resources in partnerships for branding, the marketing website, and initial design direction. However, much of this had to be discarded as we pivoted, highlighting the importance of finding product-market fit before making significant investments.
Embrace adaptability, resilience, and a willingness to fail: The startup environment taught me the value of being open-minded and flexible in the face of challenges, including multiple pivots, layoffs, redirections, and ultimately, shutting down. I learned to find clarity in ambiguous situations, and being okay with change.